-
Notifications
You must be signed in to change notification settings - Fork 169
Create Policy From MDE Advanced Hunting
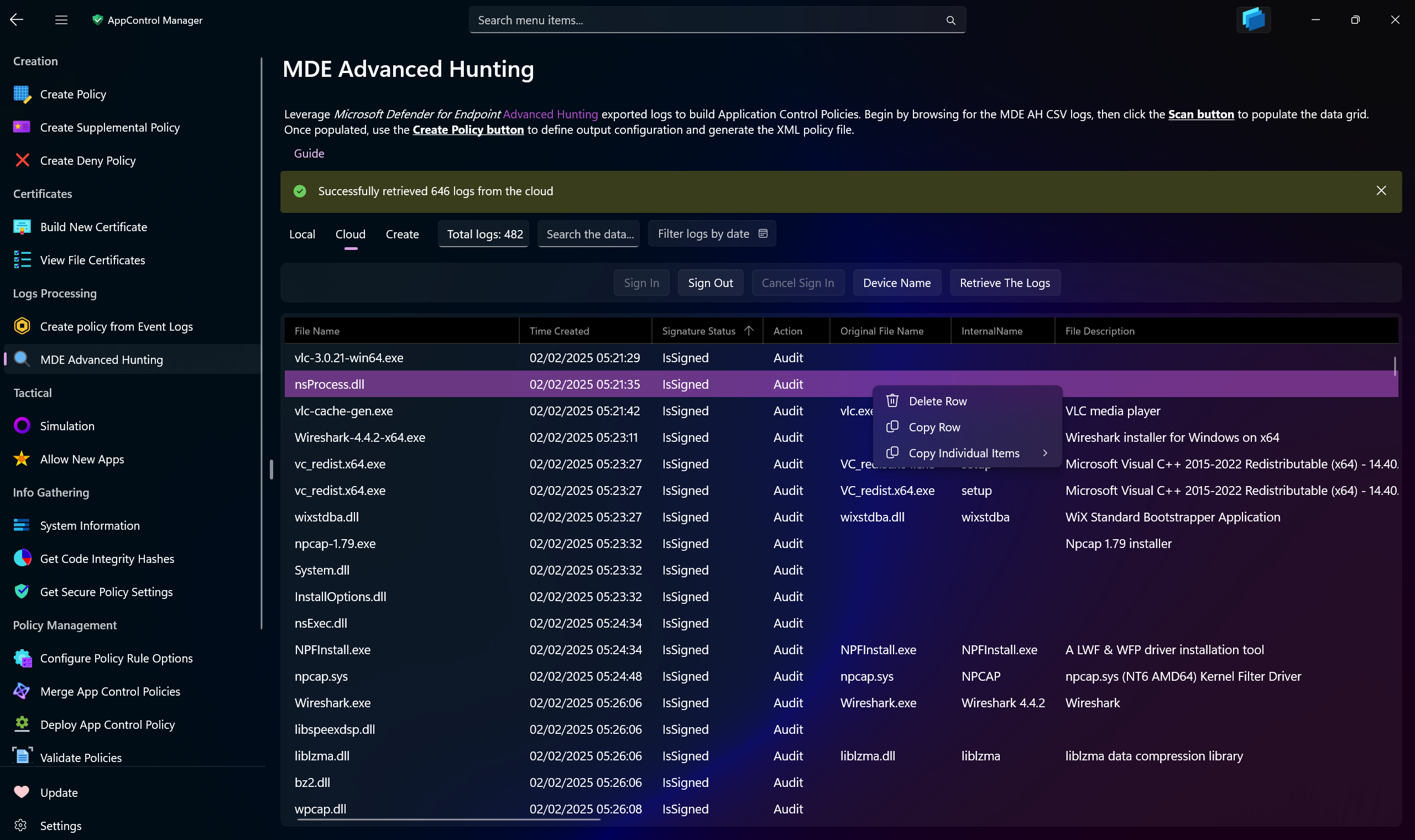
Use this AppControl Manager page to create App Control policies based on Microsoft Defender for Endpoint (MDE) Advanced Hunting exported CSV logs. Refer to this page for more information.
This page offers a data grid that has search functionality, sorting, removal of individual logs and copying entire rows or each cell to the clipboard.
You can also sign into your tenant to automatically retrieve Advanced Hunting logs related to Application Control and view, process, filter, search and convert them into App Control policies, all within the AppControl Manager application.
Performing Advanced Hunting queries requires ThreatHunting.Read.All permission.
-
Filters logs by date: Use the calendar to filter the logs based on date they were generated.
-
Search box: Use this box to search for specific logs based on any available criteria/column.
-
Scan Logs: Initially disabled until you select MDE Advanced Hunting CSV logs.
-
Browse for MDE Advanced Huntings logs: Use this button to browse for CSV files containing the Microsoft Defender for Endpoint Advanced Hunting exported CSV logs.
-
Sign In: Sign into your tenant with Entra ID credentials.
-
Sign Out: Sign out of your tenant and discard any saved credentials from the app's memory.
-
Cancel Sign In: Cancel the sign-in process. If there was a problem during sign in process, use this button to cancel it and try again by pressing the
Sign Inbutton. -
Device Name: Use this button to display a text box where you can enter a name of a device to filter the logs by before retrieving them. The device name will be included as part of the query that will be forwarded to the MDE Advanced Hunting API and the filtering will happen on the MDE side.
-
Retrieve The Logs: Use this button to retrieve the Advanced Hunting logs that are related to Application Control policies. The logs will be displayed in the data grid.
-
Create Policy -> Add to policy: Use this option to select an existing Application Control XML policy file. The events you choose will be added directly to this file, expanding its coverage.
-
Create Policy -> Base policy file: This option allows you to specify a base XML policy file. The supplemental policy generated from the event logs will be linked to this base policy.
-
Create Policy -> Base GUID: Enter the GUID of an existing base policy here. The supplemental policy created from the event logs will be associated with this specified GUID.
-
Policy Name: Enter the name of the policy that will be created from the MDE Advanced Hunting logs.
-
Scan Level: You can choose from different scan levels. Refer to this page for all the information about them.
-
Actions -> Select All: Use this option to select all the logs in the data grid.
-
Actions -> De-select All: Use this option to deselect all the logs in the data grid.
-
Actions -> Clear Data: Use this option to clear all of the processes and detected logs.
-
Actions -> Deploy Policy After Creation: Use this option to automatically deploy the App Control policy that you create with MDE Advanced Hunting logs to the local system.
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Validate Policies
- View File Certificates
- Introduction
- How To Generate Audit Logs via App Control Policies
- How To Create an App Control Supplemental Policy
- The Strength of Signed App Control Policies
- How To Upload App Control Policies To Intune Using AppControl Manager
- How To Create and Maintain Strict Kernel‐Mode App Control Policy
- How to Create an App Control Deny Policy
- App Control Notes
- How to use Windows Server to Create App Control Code Signing Certificate
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Overrides for Microsoft Security Baseline
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
